Cybersecurity Services
The Cobalt Cybersecurity Services provides security testing solutions beyond Pentesting as a Service. Our focus on process execution allows for faster engagements with a centralized view into the health of security programs and a clear path for elevated security posture.
Engagements
The Cobalt Cybersecurity Services team can run the following engagements:
- Digital risk assessment*
- IoT ecosystem pentest
- Secure code review*
- Red teaming
*Indicates engagements available to create on Cobalt. Other engagement types will be handled by request on the Catalog page.
Process
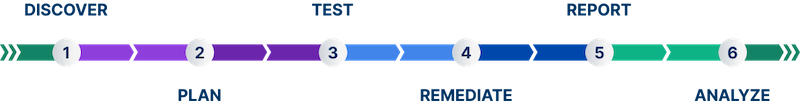
Here are the stages of a Cybersecurity Services engagement:
| Stage | Description | |
|---|---|---|
| 1 | Discover | You define what you need to test. Create an engagement brief, or make a request on the Catalog page. |
| 2 | Plan | During this stage, we will determine the scope, including the engagement type and methodology. Create a Statement of Work (if applicable) and set timelines. |
| 3 | Test | The Cobalt Cybersecurity Services team tests your asset using the determined methodology.
|
| 4 | Remediate | The testing process is complete. Remediate discovered findings.
|
| 5 | Report | We share a report once the engagement is complete. For engagements, the report sections may differ compared to standard pentests. |
| 6 | Analyze | Once the engagement is complete, analyze the security posture of your asset.
|
How to Request Cybersecurity Services
To request an IoT pentest or a Red Team engagement, navigate to the Catalog page in Cobalt. Select Request on the service you are interested in.
Our CSM team will reach out to start the process at a time that suits you. We will ask you to fill out a scoping form which will speed up the process.
Last modified June 17, 2025